Key Features
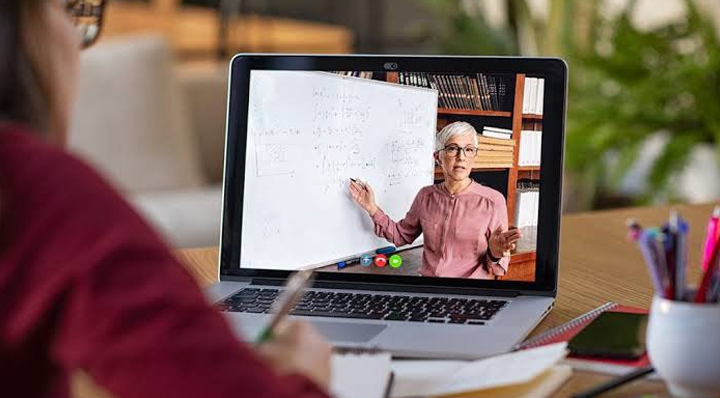
- Learn from anywhere in the world. Connect with an Instructor in real time.
- Attend Live Class from a PC or Mobile.
- Ask questions from an Instructor in real time over voice & chat.
- Includes Certificate of Completion.
- Official Exam & Certification Assitance.
- Get 30 Days free after class support.